The Massive 3CX Supply-Chain Hack Targeted Cryptocurrency Firms
North Korean hackers appear to have used the corrupted VoIP software to go after just a handful of crypto firms with “surgical precision.”
SOFTWARE SUPPLY-CHAIN ATTACKS, in which hackers corrupt widely used applications to push their own code to thousands or even millions of machines, have become a scourge, both insidious and potentially huge in the breadth of their impact. But the latest major software supply-chain attack, in which hackers who appear to be working on behalf of the North Korean government hid their code in the installer for a common VoIP application known as 3CX, seems so far to have had a prosaic goal: breaking into a handful of cryptocurrency companies.
Researchers at Russian cybersecurity firm Kaspersky today revealed that they identified a small number of cryptocurrency-focused firms as at least some of the victims of the 3CX software supply-chain attack that's unfolded over the past week. Kaspersky declined to name any of those victim companies, but it notes that they're based in “western Asia.”
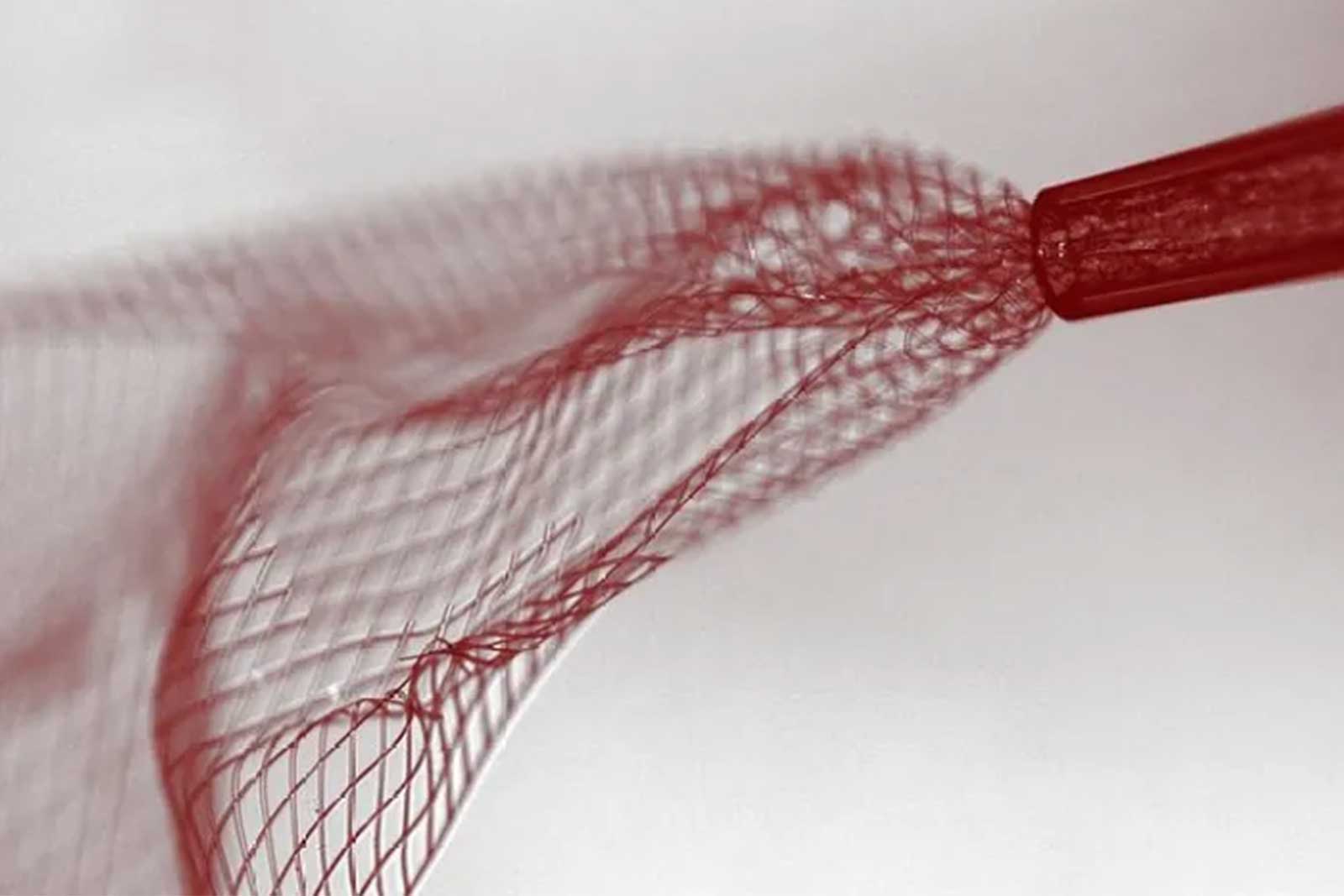
Security firms CrowdStrike and SentinelOne last week pinned the operation on North Korean hackers, who compromised 3CX installer software that's used by 600,000 organizations worldwide, according to the vendor. Despite the potentially massive breadth of that attack, which SentinelOne dubbed “Smooth Operator,” Kaspersky has now found that the hackers combed through the victims infected with its corrupted software to ultimately target fewer than 10 machines—at least as far as Kaspersky could observe so far—and that they seemed to be focusing on cryptocurrency firms with “surgical precision.”
“This was all just to compromise a small group of companies, maybe not just in cryptocurrency, but what we see is that one of the interests of the attackers is cryptocurrency companies,” says Georgy Kucherin, a researcher on Kaspersky's GReAT team of security analysts. “Cryptocurrency companies should be especially concerned about this attack because they are the likely targets, and they should scan their systems for further compromise.”
Kaspersky based that conclusion on the discovery that, in some cases, the 3CX supply-chain hackers used their attack to ultimately plant a versatile backdoor program known as Gopuram on victim machines, which the researchers describe as “the final payload in the attack chain.” Kaspersky says the appearance of that malware also represents a North Korean fingerprint: It has seen Gopuram used before on the same network as another piece of malware, known as AppleJeus, linked to North Korean hackers. It's also previously seen Gopuram connect to the same command-and-control infrastructure as AppleJeus, and has seen Gopuram used previously to target cryptocurrency firms. All of that suggests not only that the 3CX attack was carried out by North Korean hackers, but that it may have been intended to breach cryptocurrency firms in order to steal from those companies, a common tactic of North Korean hackers ordered to raise money for the regime of Kim Jong-Un.
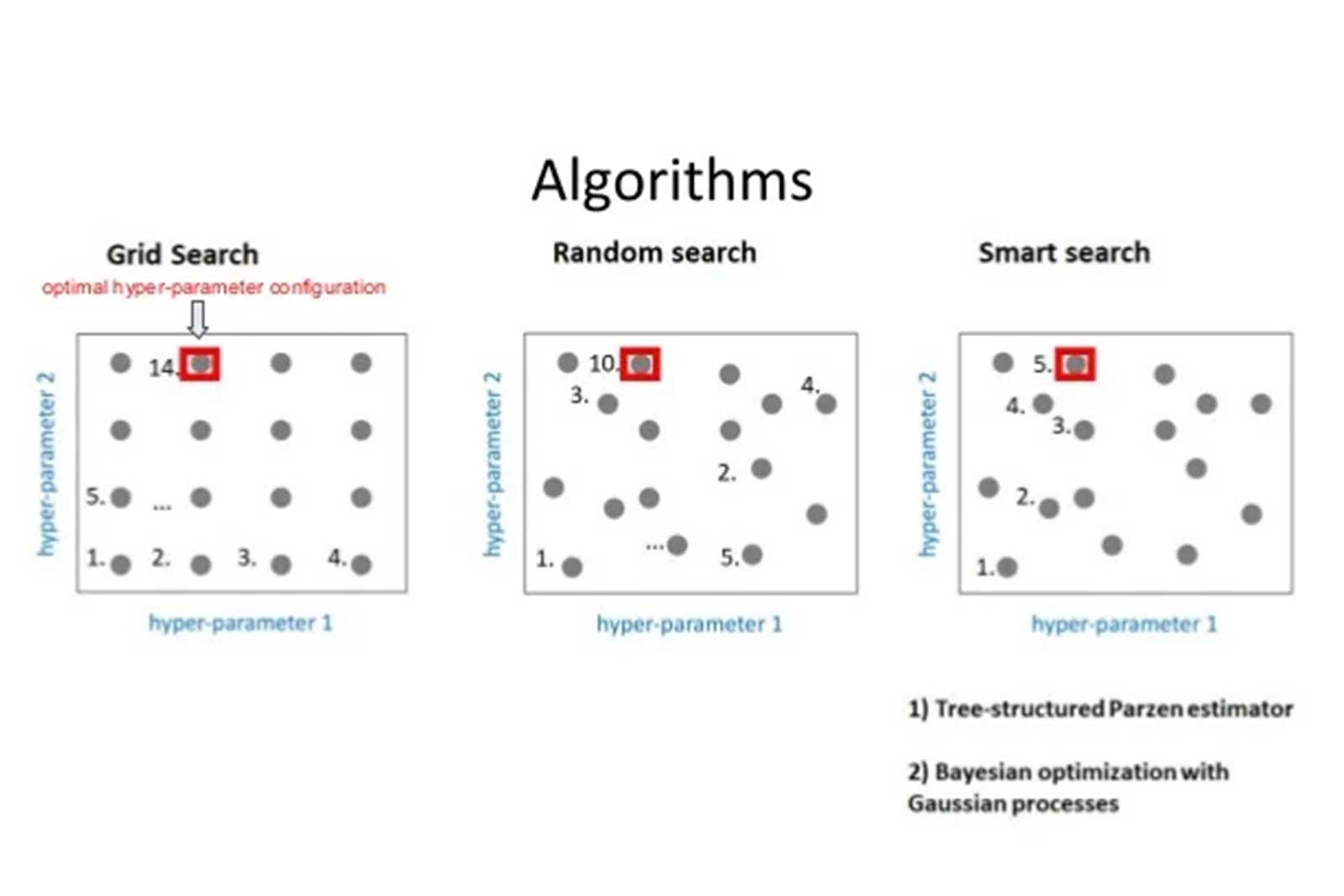
It has become a recurring theme for sophisticated state-sponsored hackers to exploit software supply chains to access the networks of thousands of organizations, only to winnow their focus down to a few victims. In 2020's notorious Solar Winds spy campaign, for instance, Russian hackers compromised the IT monitoring software Orion to push malicious updates to about 18,000 victims, but they appear to have stolen data from only a few dozen of them. In the earlier supply chain compromise of the CCleaner software, the Chinese hacker group known as Barium or WickedPanda compromised as many as 700,000 PCs, but similarly chose to target a relatively short list of tech firms.
“This is becoming very common,” says Kucherin, who also worked on the SolarWinds analysis and found clues linking that supply-chain attack to a known Russian group. “During supply-chain attacks, the threat actor conducts reconnaissance on the victims, collecting information, then they filter out this information, selecting victims to deploy a second-stage malware.” That filtering process is designed to help the hackers avoid detection, Kucherin points out, since deploying the second-stage malware to too many victims allows the attack to be more easily detected.
But Kucherin notes that the 3CX supply-chain attack was nonetheless detected relatively quickly, compared to others. The installation of the initial malware that the hackers appeared to use for reconnaissance was detected by companies like CrowdStrike and SentinelOne last week, less than a month after it was deployed. “They tried to be stealthy, but they failed,” Kucherin says. “Their first-stage implants were discovered.”
Given that detection, it's not clear how successful the campaign has been. Kucherin says Kaspersky hasn't seen any evidence of actual theft of cryptocurrency from the companies it saw targeted with the Gopuram malware.
But given the hundreds of thousands of potential victims of the 3CX supply-chain compromise, no one should conclude yet that crypto companies alone were targeted, says Tom Hegel, a security researcher with SentinelOne. “The current theory at this point is that the attackers did initially target crypto firms to get into those high-value organizations,” Hegel says. “I’m going to guess that once they saw the success of this, and the kinds of networks they were in, other objectives probably came into play.”
For now, Hegel says, no single security firm can see the whole shape of the 3CX hacking campaign or definitively state its goals. But if North Korean hackers really did compromise a piece of software used by 600,000 organizations around the world and use it just to try to steal cryptocurrency from a handful of them, they may have thrown away the keys to a much larger kingdom.
“This is all unfolding very quickly. I think we’ll continue to gain better insight into the victims,” Hegel says. “But from an attacker standpoint, if all they did was target crypto firms, this was a dramatic wasted opportunity.”